AGIX Linux Cybersecurity
Cybersecurity is a priority for networks and organizations, especially in industries that handle sensitive information. The certified Linux cybersecurity experts at AGIX are trusted professionals when it comes to keeping networks and systems safe from harm. Whether you need to protect sensitive information from outside interference or just keep hackers out of your network, AGIX has the experience that can help.
Security Experts That You Can Trust
AGIX’s professional team has the experience that you can count on when it comes to cybersecurity. Having worked with organizations in high-security industries such as Defence and Finance, we understand the intricacies of keeping information secure from an unexpected attack. With our years of experience, we can be trusted with the most sensitive information in your network.
We Take Cybersecurity Seriously
Our experienced professionals at AGIX are highly equipped to handle every aspect of cybersecurity. Working with sensitive information requires more than just careful planning and serious oversight; we also conduct extensive testing in every step of the way, and ensure that everything is up-to-date by our clients’ exacting standards. Consult with us and see why our clients trust us with even the most complex security concerns.
Contact our friendly team to get started.
This article demonstrates how to configure HAProxy to use LetsEncrypt to automatically manage certificates ensuring that those on the Internet accessing servers behind your HAProxy are protected with SSL security. Here’s some important points before we get started: We’re using a Netgate pfSense firewall appliance in this example but pfSense
Read more
This article is focused on generating a CSR file, submitting it to a CA and using the resulting Certificate on Linux with Apache, Nginx and/or IIS on Windows. The Windows related steps continue on from the work required to get the Certificate ready for Linux. In other words, regardless of
Read more
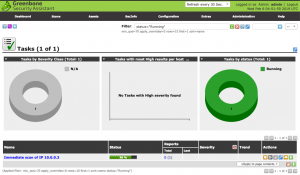
Don’t bother trying to install OpenVAS. Instead, download the trial ISO image and use that. HowTo’s you’ve probably already read all discuss installing OpenVAS by compiling it yourself. It seems installing via package managers is a thing of the past. I hope this changes – or that i and so
Read more
This article demonstrates how to use Fail2Ban to block IP addresses attempting to compromise a WordPress instance via the login process. In this walk-through, we’re using CentOS 7 and FirewallD. Just be aware that if you’re using a caching service like CloudFlare, you can’t use this method because you’ll block
Read more
This article demonstrates how to install the new Tsunami vulnerability scanner on a Redhat-like machine such as Fedora or CentOS 8 and how to use it including an example script to scan multiple targets or subnets. Install Java: yum install java-*-openjdk-devel Download the Tsunami ZIP from here: https://github.com/google/tsunami-security-scanner/archive/master.zip Extract the
Read more
This article demonstrates one way to get and crack Windows 10 passwords. All the steps are completed on Windows 10. The last step of running the hashes through the Rainbow attack process could be replaced with John (JtR). The tools we’ll use are: Windows 10 Pro samdump2 mimikatz https://crackstation.net Step
Read more
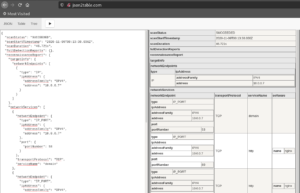
This article demonstrates how to generate a CSR (certificate signing request) using OpenSSL. In the examples below, change the bold text to be correct for you. Generate the key file: openssl genrsa -out example.key 2048 && chmod 0600 example.key Create the config file as “/etc/httpd/example.csr.conf: [ req ] default_bits =
Read more
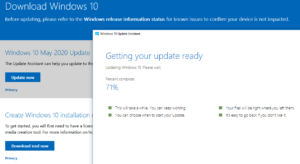
Trouble installing Windows 10 Updates? This article is for you. Visit the site: https://www.microsoft.com/en-us/software-download/windows10 … and click the “Update Now” button. The program that downloads helps you manually update Windows. Execute it and go through the Wizard. Warning, this takes your computer into a process of uninterruptible reboots and updates
Read more
This article explains how to install OpenVAS on Kali Linux. The difference between this method and others is the switch from “openvas” to “gvm” for naming/marketing. As you might have seen, I’ve written several articles on installing and using OpenVAS on CentOS. Don’t do it. Don’t go through the pain
Read more
This is a short article focused on helping you protect your wireless network from hackers. The AirCrack-NG suite is the most common set of tools used to crack wireless networks. For that reason, we’re focused on that suite for this article. Other tools need to deal with the same wireless
Read more