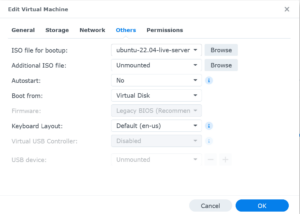
This article shows the correct settings to use for running a Ubuntu Linux virtual machine on the Synology NAS. The default settings wont work, but with a few adjustments, you can easily run Ubuntu Linux virtualization on a Synology NAS. The virtual machine manager settings windows should look similar to
Read more