Get help with Ubuntu, Mint and Debian Linux Distributions. AGIX staff have the know-how and experience to help your organisation with best-practices, current technology in various Cloud environments including Amazon AWS.
AGIX is a Canonical (Ubuntu) Partner. We study, sell and support Ubuntu Linux.
This page shows examples of our work that AGIX shares freely with you. For a fully supported compute environment, contact our team to find out how we can help your organization move forward in the right way.
Contact our friendly team to get started.
This article holds my notes from when I recently tested the Redhat Ansible Automation Platform. I’ve included answers to the questions I had at the start and during my effort to install the system. You need to install this on a Redhat Enterprise Linux v8.4 server, or newer. You don’t
Read more
Long-time Linux system administrators typically use the “ifconfig” command. Perhaps out of habbit, or because it works on other OS’s (similar to ipconfig on Windows). But we should be using the “ip” command in-place of “ifconfig”. The “net-tools” package needs to be installed if you want the “ifconfig” command, and
Read more
In this article we’re going to walk through installing Docker on Ubuntu, starting a few Docker containers, and then running those containers behind a reverse proxy. When we’re done, you’ll have a load balance terminating SSL (TLS) connections with multiple Docker containers running the workload. This is how it will
Read more
This article shows how to implement a small Node.js application that pulls data from a local MySQL server. We’re doing this on a CentOS server but that’s not important – any Linux will do. But if you’re using Windows, the installation process will differ. yum install nodejs npm install mysql
Read more
The modules that we use are specific to our needs. But these are the most commonly used from my recent history. This list is super generic and mostly to supplement my poor memory. These methods/modules rely on a previously completed db_nmap scan. So our targets are readily available from the
Read more
If you want to create a customised password list for a specific target (client, I hope), this article is for you. It’s basically just a re-write of “https://karimlalji.wordpress.com/2018/04/26/password-guessing-mangle-a-custom-wordlist-with-cewl-and-hashcat/” which I’ll probably forget later so I’m documenting here. We don’t just want a list of passwords, we want a list of
Read more
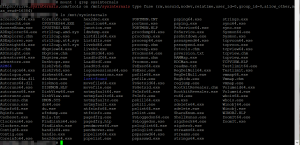
This article demonstrates how to mount “https://live.sysinternals.com/tools” on Linux so that it’s accessible at “/mnt/sysinternals”, for example. On CentOS: yum install davfs2 On Ubuntu: apt install davfs2 Mount it: mount -t davfs https://live.sysinternals.com/tools /mnt/sysinternals Now you can access it at: # ls /mnt/sysinternals/ accesschk64.exe diskext.exe pipelist.exe RegDelNull.exe accesschk.exe Diskmon.exe PORTMON.CNT
Read more
This article is mostly a cheat sheet for things pen-testers need. Obviously there’s a little picking and choosing depending on the need. Nmap: Ubuntu: apt install nmap CentOS: yum install nmap Nikto: Ubuntu: apt install nikto CentOS: yum install nikto Mimikatz: https://sourceforge.net/projects/mimikatz.mirror/files/latest/download Hydra: Ubuntu: apt install hydra Cewl: Ubuntu: apt
Read more
This article walks you through the process of installing, configuring and running scans using Metasploit and Nmap. Both CentOS 7 and Ubuntu 20.04 are discussed. Our objective is to be able to run nmap scans and have the results go into a database so we can filter the results later
Read more
This article demonstrates how to use Ubuntu booted from a USB disk to do WIFI penetration testing. Why would you want to do this? If you have Windows on your laptop and need to use Aircrack-NG, you’ll need to fight with wireless adapter driver issues. So you’ll try Kali Linux
Read more