Get help with Redhat Enterprise Linux, Fedora and CentOS Linux Distributions. AGIX staff have the know-how and experience to help your organisation with best-practices, current technology in various Cloud environments including Amazon AWS.
AGIX is a Redhat Partner. We study, sell and support Redhat Enterprise Linux.
This page shows examples of our work that AGIX shares freely with you. For a fully supported compute environment, contact our team to find out how we can help your organization move forward in the right way.
Contact our friendly team to get started.
This article demonstrates how to use Fail2Ban to block IP addresses attempting to compromise a WordPress instance via the login process. In this walk-through, we’re using CentOS 7 and FirewallD. Just be aware that if you’re using a caching service like CloudFlare, you can’t use this method because you’ll block
Read more
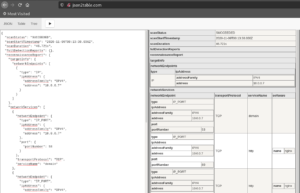
This article demonstrates how to install the new Tsunami vulnerability scanner on a Redhat-like machine such as Fedora or CentOS 8 and how to use it including an example script to scan multiple targets or subnets. Install Java: yum install java-*-openjdk-devel Download the Tsunami ZIP from here: https://github.com/google/tsunami-security-scanner/archive/master.zip Extract the
Read more
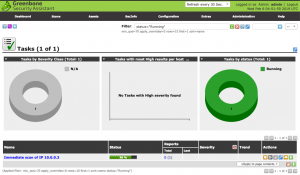
This article explains how to install OpenVAS on Kali Linux. The difference between this method and others is the switch from “openvas” to “gvm” for naming/marketing. As you might have seen, I’ve written several articles on installing and using OpenVAS on CentOS. Don’t do it. Don’t go through the pain
Read more
This article demonstrates how to crack a wireless network using the AirCrack-NG suite. Note that this will only work with WPA/WPA2 PSK wireless networks. That’s the limits of this generation of the AirCrack-NG suite. Only do this on a network that you own or are responsible for and have permission
Read more
This article is quick walk-through explaining how to install Bitwarden on Fedora 32 but should work on CentOS 7 and 8 as well as RHEL. Install the docker packages: yum install docker docker-compose systemctl enable docker systemctl restart docker Download the Bitwarden scripts: curl -Lso bitwarden.sh https://go.btwrdn.co/bw-sh chmod +x bitwarden.sh
Read more
This article shows how to install and run Nmap using the Vulscan add-on to do vulnerability assessments. Download Nmap: yum install nmap Install the Vulscan.nse script: /usr/share/nmap git clone https://github.com/scipag/vulscan vulscan Run a scan targeting the machine (in this example) “192.168.4.250”: nmap -sV –script vulscan/vulscan.nse 192.168.4.250 My output looks like
Read more
This article shows how to install and run Nmap using the Vulners script to do vulnerability assessments. Download Nmap: yum install nmap Install the Vulners.nse script: /usr/share/nmap wget https://svn.nmap.org/nmap/scripts/vulners.nse Run a scan targetting the machine (in this example) “192.168.4.250”: nmap -sV –script vulners.nse 192.168.4.250 My output looks like this: 22/tcp
Read more
This article demonstrates how to install and configured FreeRadius for basic authentication. By “basic authentication”, I mean we’re going to configure local users in clear text. This is the simplest way to configure FreeRadius. We’re installing this on CentOS 8. Install the software: yum install freeradius freeradius-utils Add the client
Read more
This article is a short walk-through demonstrating the process of installing and configuring mod_security on Apache. In this tutorial, we’ll be using CentOS 7. We’re starting with a pre-configured and running web server running httpd listening on port 80 and 443. There’s no other services such as Varnishor Nginx running.
Read more
This article is a quick note on how to improve OpenSSH server security on Redhat Enterprise Linux and CentOS 6 and 7. This is not about Passwords-v-Keys (use keys, not passwords) but rather hashes, encryption and key exchanges. The “/etc/ssh/sshd_config” file should have the following added to it to ensure
Read more