There are two issues with creating EC2 snapshots on a schedule. First the AWS recommended way doesn’t allow for custom names for snapshots which we use for identifying the source or schedule. Second the AWS IAM doesn’t have a built-in policy that allows it. So this article provides an example
Read moreGet help with Linux, Automation, Cybersecurity and more. AGIX staff have the know-how and experience to help your organisation with best-practices, current technology in various Cloud environments including Amazon AWS. Our technicians support Ubuntu, Redhat, Databases, Firewalls, Ansible and Terraform, Storage and more.
This page shows examples of our work that AGIX shares freely with you. For a fully supported compute environment, contact our team to find out how we can help your organization move forward in the right way.
Contact our friendly team to get started.

IPSec/L2TP VPN on AWS EC2 | Security Group Settings
This article notes the AWS EC2 Security Group that should be associated with an EC2 to permit a roaming VPN client to connect to an IPSec/L2TP hosted on a server within AWS. * TIP: The AH and ESP are entered in as just numbers, not the “AH” and “ESP”.
Read more
Hardening SSH Server on CentOS or RHEL 6 & 7
This article is a quick note on how to improve OpenSSH server security on Redhat Enterprise Linux and CentOS 6 and 7. This is not about Passwords-v-Keys (use keys, not passwords) but rather hashes, encryption and key exchanges. The “/etc/ssh/sshd_config” file should have the following added to it to ensure
Read more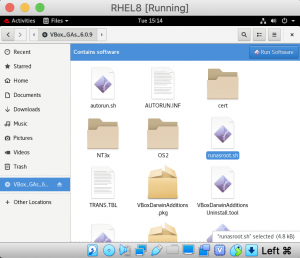
Red Hat Enterprise Linux 8 on VirtualBox
This article focuses on installing and running RHEL8 (Red Hat Enterprise Linux 8) on VirtualBo. Specifically, this article demonstrates how to install additional driver support to ensure RHEL8 mouse movements and resolutions acre correct. You can see another good article at “https://developers.redhat.com/rhel8/install-rhel8-vbox/”. This article starts from a complete installation of
Read more
Minimal Transparent Squid Proxy with SSL Interception/Bumping on CentOS 7
This article is the minimal configuration for a Squid transparent proxy with SSL Interception (or bump). We’re using CentoOS 7. This article is based on the good work at “https://www.sbarjatiya.com/notes_wiki/index.php/Configure_squid-3.3_in_transparent_mode_on_CentOS_7_with_SSL_bump” with a few minor changes/corrections. Disable SELinux or put it in permissive mode. Squid works on odd ports. I will
Read more
Zabbix Dealing with Cannot create semaphore set No space left on device
If you get this strange error when trying to start the Zabbix agent on a CentOS 7 or similar system, this article should help you solve the problem. The article at “https://www.zabbix.com/forum/zabbix-troubleshooting-and-problems/355498-centos-7-zabbix-3-4-7-cannot-create-semaphore-28-no-space-left-on-device” explains the issue further. However, you can jump right to the solution in “this” article. Issuing the command:
Read more
Install FreeIPA on CentOS 7 For LDAP and Kerberos Services
If you need a quick LDAP and Kerberos system up and running to provide authentication and user information, FreeIPA is for you. IPA is documented at “https://www.freeipa.org/page/Main_Page”. This article demonstrates how to set up FreeIPA on CentOS 7. By the end of this article, you’ll have a working FreeIPS system
Read more
How to Configure AutoFS on RHEL/CentOS 7 | RHCSA
This article shows how to configure a Redhat/CentOS 7 workstation to access a remote storage system using both NFS and CIFS. This article focuses on the workstation (client) side. The server should already be configured to share the resources. For this demonstration, the following detalis need to be know about
Read more
Remove Adverts from vTigerCRM (2019)
vTigerCRM is an excellent opensource (free to use) CRM that I use. However, it does have a small advert to help promote the work of 3rd party developers contributing the to marketplace. It’s there for a good reason but i fully understand why some people don’t want it there. You
Read more
Automatically Detect and Block Port Scanning With pfSense and Snort
High-end firewall appliances such as those from Watchguard offer the facility to automatically block remote systems based on their behavior such as port scanning. An intruder will often start their intrusion with some reconnaissance which includes scanning the remote system for open ports to learn what services are available. pfSense
Read more